The Lincoln Family of
Companies History:
The Lincoln Family of Companies was formed by John Palisano and his six sons in 1914. The company started in a Niagara Street horse stable with one horse and
one wagon.
The continued focus on quality, storage, transportation and delivery has enable the company to success and expand over the past 100 years. Today, the Lincoln Family of Companies includes the companies of Lincoln Moving & Storage, Lincoln Self Storage, Lincoln Warehousing Company, WNY Foreign Trade Zone Operators, Inc., and Biosan Disposal, LLC.
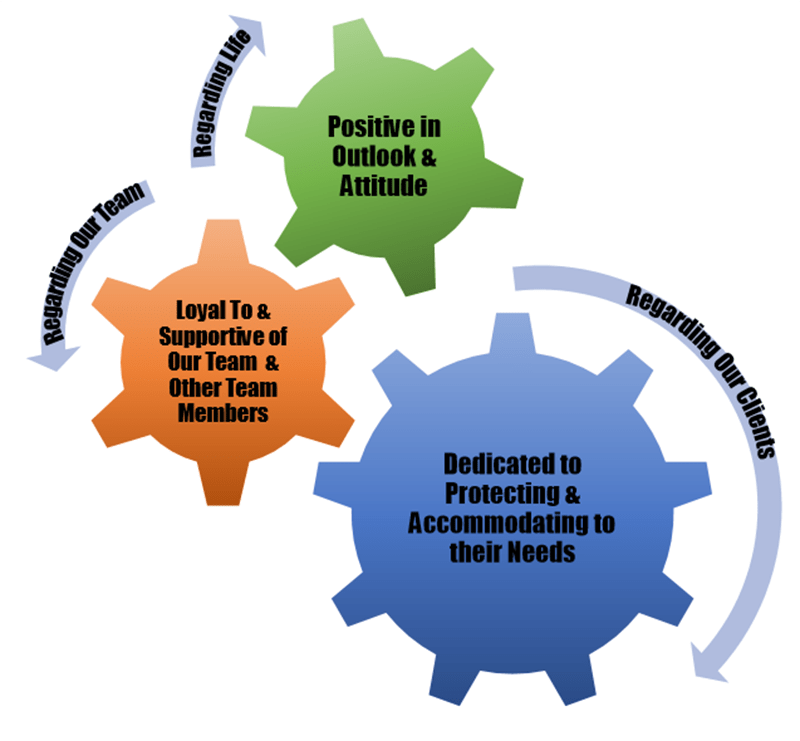
Lincoln Archives: Our Core Values
Serving Western New York Families & Businesses for over 100 years
Take a 40 Second Tour of our Company
Get Your Quote
"*" indicates required fields
Resources
Call for Service Today!
Ready to protect your organization's sensitive information with professional document security services?
Contact Lincoln Archives at (716) 871-7040 or complete the form on this page to discuss your specific location and service requirements. Our experienced team will develop a customized solution that meets your compliance needs while providing the security and reliability your organization deserves.
Get started today with Western New York's most trusted document security provider.

